The Emotet malware is owning a burst in distribution and is probable to soon switch to new payloads that are at the moment detected by much less antivirus engines.
Protection researcher monitoring the botnet are observing that email messages carrying destructive payloads last thirty day period have amplified tenfold.
Emotet is a self-propagating modular trojan that can manage persistence on the host. It is utilised for stealing person information, accomplishing network reconnaissance, going laterally, or dropping further payloads these as Cobalt Strike and ransomware in particular.
It has been spotted increasing slowly but steadily because the commencing of the year, but its operators may be shifting up a equipment now.
Spike in distribution
In accordance to a report Kaspersky launched these days, Emotet action is viewing a sharp rise from February to March, likely from 3,000 to 30,000 e-mails.
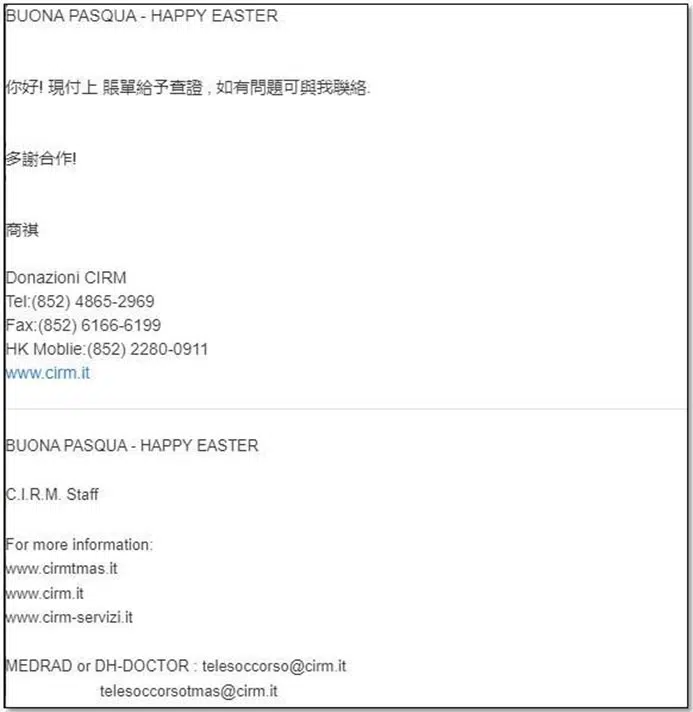
The languages used in these messages include English, French, Hungarian, Italian, Norwegian, Polish, Russian, Slovenian, Spanish, and Chinese.
As for the themes, Emotet distributors are regarded for altering the subject areas regularly to consider advantage of seasonal interest swifts. This time it’s the Easter celebration they’re taking benefit of.
Check Stage also produced a report, which ranked Emotet as the range 1 most widespread and active malware in March 2022.
(Look at Issue)
Kaspersky mentions that the ongoing Emotet e-mail distribution strategies also make use of dialogue thread hijacking methods, observed in Qbot strategies joined to the similar operators.
“Cybercriminals intercept by now existing correspondence and mail the recipients an e-mail that contains a file or link, which frequently prospects to a legitimate well-known cloud-internet hosting assistance,” Kaspersky
“The aim of the electronic mail is to encourage consumers to possibly (i) adhere to the connection and down load an archived doc and open it – in some cases utilizing a password pointed out in the e-mail, or (ii) simply just open an e-mail attachment,” the researchers be aware.
For the reason that the threat actors have access to prior correspondence, it is moderately easy for them to existing the attachment as some thing the recipient would anticipate as a continuation of the dialogue with colleagues.
Swap to 64-little bit
The Cryptolaemus stability analysis group, who is retaining a sharp eye on Emotet botnet action, claimed that the malware operators have also switched to 64-bit loaders and stealer modules on Epoch 4, just one of subgroups of the botnet that run on individual infrastructure. Previously, it relied on 32-little bit code.
#Emotet Update – Seems to be like Ivan laid an egg for easter and has been occupied. As of about 14:00UTC right now 2022/04/18 – Emotet on Epoch 4 has switched above to utilizing 64-bit loaders and stealer modules. Earlier every little thing was 32-bit apart from for occasional loader shenanigans. 1/x— Cryptolaemus (@Cryptolaemus1) April 19, 2022
The switch is not obvious on Epoch 5 but the hold off is anticipated, since Epoch 4 generally serves as a development check-mattress for the Emotet operators, researchers from Cryptolaemus say.
Currently, the detection rate for Epoch 4 has dropped by 60%, which is thought to be a immediate consequence of this modify.
